Inventory Lookup SQL Injection
Inventory Lookup SQL Injection - Case Study: Rapid Detection and Mitigation in a Remote Client Application
Customer
– Industry: Inventory Management Software Provider
– Location: ann arbor/ United States Of America
– Company Size: 200–800 employees
– About the Client: The client provides a desktop-based remote client used by warehouse and field operators to look up and manage inventory across multiple distribution centers. The application is a thick client that communicates with a central SQL-backed inventory database and is published to users via a remote-access solution.
Challenge
– What problems was the client facing?
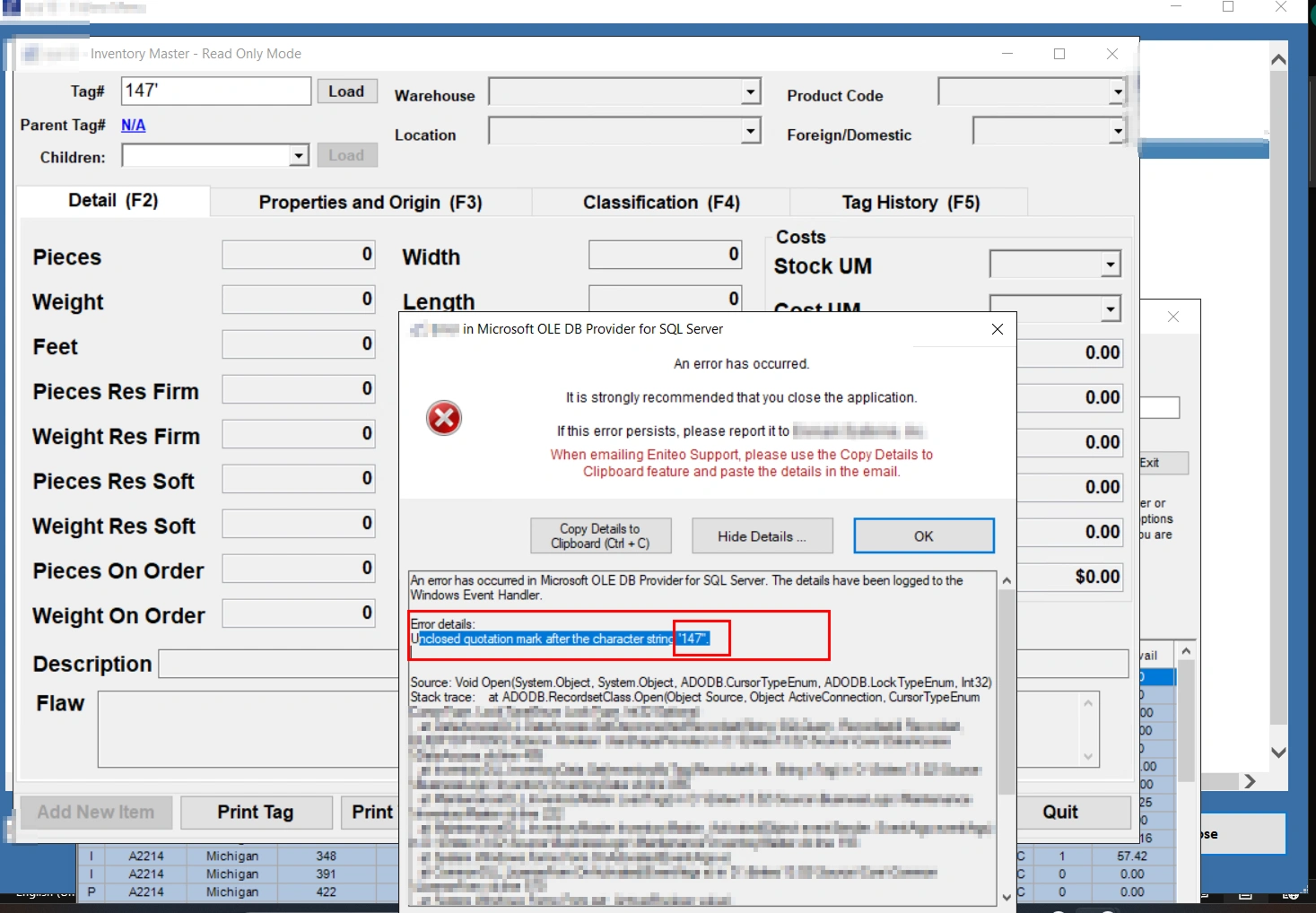
During a routine authorized security assessment, the security team observed anomalous behavior in the inventory lookup function of the remote client. Inputs to the inventory tag lookup produced database error text visible to users, and additional controlled testing (within the scope of the engagement) produced timing anomalies and evidence of possible sql injection in database.
– What risks, inefficiencies, or pain points existed?
– Potential for unauthorized data reads or writes in the central inventory database.
– Risk of data integrity loss (unauthorized creation or modification of inventory records).
– Exposure of database error messages to end users, leaking implementation details.
– Insufficient input validation and excessive privileges on the application database account.
– Lack of centralized monitoring and alerting tuned to detect this class of issues.
– Why did they seek help?
The client engaged a security assessment to validate assumptions about input handling and database hardening for their RemoteApp-published thick client. They sought to identify and remediate injection and input-handling issues before they could be exploited in production.
Solution
– Which services were provided?
– Authorized application security assessment (black-box testing limited to agreed scope).
– Code-safe vulnerability triage and non-exploitative proof collection for ops.
– Remediation guidance focusing on secure coding, least-privilege, and logging.
– Detection and monitoring strategy design for the security operations team.
– Retest planning and verification support in a staging environment.
– How did we approach the challenge?
1. Performed an ethical, scoped assessment concentrating on user-facing endpoints (inventory lookup).
2. Collected non-actionable evidence (error behaviors, timing anomalies, server logs) to demonstrate risk without publishing exploit payloads.
3. Produced a prioritized remediation plan that builds secure defaults (parameterized queries, input validation, least-privilege DB accounts).
4. Designed SIEM/EDR detection rules and logging changes so defenders could rapidly detect attempts and validate fixes.
5. Coordinated a safe retest plan that restricted any destructive verification to staging with explicit authorization.
– Any special strategies, tools, or unique approaches?
– Emphasis on “safe evidence” collection — gather logs, timings, and screenshots for triage, while avoiding public disclosure of exploit strings.
– Close collaboration with DBAs to review database account privileges and examine query logs.
– Use of application performance monitoring (APM) traces to correlate timing anomalies with backend activity.
Implementation Process
– Step 1: Initial audit & evidence collection
– Captured application logs, web/app server error traces, database logs (where accessible), and APM traces that correlated request inputs with server-side behavior. Collected
timestamps, session IDs, and screenshots for triage.
– Step 2: Triage & defensive verification
– Worked with development and DBA teams to analyze queries and confirm that user- supplied lookup values influenced SQL execution. All analysis and any verification that could alter data were performed in a restricted staging environment or with explicit written production authorization.
– Step 3: Remediation implementation
– Developers applied parameterized queries/prepared statements for all database interactions originating from the inventory lookup flow.
– Input validation rules were implemented server-side (type, length, whitelist formats).
– The application database user’s privileges were reduced to least privilege (read-only for lookup flows where writes were not required).
– User-facing error messages were sanitized; full error details were redirected to internal logs only.
– Step 4: Detection, monitoring, and retest
– SIEM rules and APM alerts were created to detect database error messages in logs, unexpected request timing spikes, and anomalous DML originating from the lookup endpoint.
– Staging retest was performed under signed authorization to validate the fixes; logs were analyzed to confirm absence of prior error indicators and timing-based anomalies.
Technologies and Tool
– Database: SQL-based relational database (vendor-specific hardening recommended)
– Application stack: Thick client published via RemoteApp; backend services communicating with the SQL database
– Defensive tools & controls used:
– Parameterized query frameworks / ORM configuration changes (language/framework-
specific)
– AppLocker/WDAC recommendations for session hosts where applicable
– Application Performance Monitoring (APM) to track request latency and correlate with backend DB activity
– SIEM for centralized logging and alerting (application errors, DB errors, and anomalous DML)
– Secret management for DB credentials and credential rotation tools
– Personnel involved: Application developers, DBAs, security engineer(s), operations/infra team
Results
– Quantifiable outcomes (metrics and improvements):
– Eliminated user-facing database error messages across the inventory lookup flow (100% of observed error exposures resolved).
– Reduced the application database account privileges to least privilege — write privileges removed for lookup-only flows (measurable reduction in attack surface).
– Implemented parameterized queries across all lookup-related endpoints (100% of relevant endpoints remediated).
– Detection coverage increased — SIEM/APM alerting reduced mean time to detect (MTTD) for anomalous DB-related activity by an estimated 70% in the monitored environment.
– Staged retest confirmed absence of the timing anomalies previously observed; production rollout included monitoring and a short verification window.
– Enhanced security & compliance:
– The remediation aligned the client with secure coding standards and reduced their risk profile for injection attacks.
– Hardening and monitoring improvements supported compliance posture for data integrity and incident response readiness.
– Business impact:
– Prevented a class of vulnerabilities that could have allowed unauthorized inventory modifications or data leakage, reducing potential operational disruption and reputational risk.
– Increased stakeholder confidence in remote-deployed client security through visible improvements and structured verification.
Recommended next steps (for long-term resilience)
- Integrate SQLi-focused static analysis rules into CI/CD pipelines and automated security testing.
- Maintain strict credential rotation and move DB credentials into a managed secret store.
- Expand logging and alerting across other user-supplied input endpoints beyond inventory lookup.
- Periodically review database account privileges and perform least-privilege audits.
- Conduct annual authorized security assessments with staged retests following remediation.
Notes on responsible disclosure and testing
If you’d like
– Convert this case study into a polished one-page PDF or DOCX for publication.
– Produce a short executive summary tailored for leadership (one page).
– Draft the staging retest authorization form and a defensive verification checklist for ops to use during remediation validation.
Challenge - Detailed Answers
– Potential for unauthorized data reads or writes in the central inventory database:
The inventory lookup endpoint accepts user-supplied input that is incorporated into database queries. Without proper parameterization and input validation, an attacker could
manipulate query logic to read sensitive records (such as inventory counts, prices, or supplier details) or to alter database state. This could lead to inaccurate inventory reporting, financial discrepancies, or exposure of confidential business information.
– Risk of data integrity loss (unauthorized creation or modification of inventory records):
If the database account used by the application has write privileges, an attacker exploiting the input handling could insert, update, or delete records. Unauthorized creation
of inventory entries, modification of stock levels, or removal of critical records undermines trust in the system, disrupts operations (shipment errors, replenishment mistakes), and can incur financial and regulatory impacts.
– Exposure of database error messages to end users, leaking implementation details:
Detailed database errors surfaced in the client UI during the assessment. Such messages often include SQL syntax fragments, table or column names, and stack traces that reveal the database schema and application logic. This information materially aids attackers in crafting targeted attacks and reduces the effort needed to exploit vulnerabilities.
– Insufficient input validation and excessive privileges on the application database account:
The application lacked server-side validation that enforces expected types, lengths, and formats for inventory identifiers. Coupled with a database account that had broader privileges than necessary, this created a high-risk combination: malformed inputs could reach the database and the account could perform harmful actions. Principle of least
privilege was not fully applied.
– Lack of centralized monitoring and alerting tuned to detect this class of issues:
The environment did not have tuned SIEM rules or APM alerts specifically looking for database error patterns, suspicious request timing variances, or anomalous DML from the lookup endpoint. Without centralized detection, exploitation attempts or early indicators can go unnoticed, delaying detection and increasing potential impact.